DNSCrypt
DNSCrypt offers a way to protect clients against attacks related to the modification and manipulation of DNS traffic — The main objective of DNSCrypt is authentication of the communication channel between the client (you) and a resolver supporting the protocol — This will protect the client fromman in the middle attacks. In addition, encryption of DNS communication improves the client’s privacy. DNSCrypt is the client-side version ofdnscrypt-wrapper.
DNSCrypt verifies that responses you get from a DNS provider have been actually sent by that provider, and haven’t been tampered with.
This is not a VPN. It doesn’t mask your IP address, and if you are using it with a public DNS service, be aware that it will (and has to) decrypt your queries.
If you are using it for privacy, it might do the opposite of what you are trying to achieve. If you are using it to prevent VPN “leaks”, this isn’t the right tool either: the proper way to prevent VPN “leaks” is to avoid sending data to yet another third party: use a VPN service that operates its own DNSresolvers.
Installation
dnscrypt-proxy and libsodium is in the official repository for Chaos Calmer 15.05 and up.
opkg update opkg install dnscrypt-proxy
-
If installed skip to configuration.
-
If somehow you can’t install it that way, proceed with the following instructions.
ar71xx and Barrier Breaker
The OpenWrt package for ar71xx is maintained by black-roland.
Differences with OpenWrt packages:
| Package | Difference |
|---|---|
dnscrypt-proxy |
Newest version for Chaos Calmer. Barrier Breaker support. Procd support and possibility of launching multiple instances. |
libsodium |
Newest version for Chaos Calmer. Barrier Breaker support. |
iodine |
Memory usage reduce patch. |
This will install dnscrypt-proxy as well as any dependent libraries such as libsodium
Add third-party source to your opkg configuration file /etc/opkg.conf according to your OpenWRT version.
Chaos Calmer:
cd /tmp wget 'http://exopenwrt.roland.black/exopenwrt.pub' opkg-key add exopenwrt.pub echo 'src/gz exopenwrt http://exopenwrt.roland.black/chaos_calmer/15.05/ar71xx/packages/exopenwrt/' >> /etc/opkg.conf
Barrier Breaker:
http://exopenwrt.roland.black/barrier_breaker/14.07/ar71xx/packages/exopenwrt
And proceed with the installation itself:
opkg update opkg install dnscrypt-proxy
Configuration
DNSCrypt is listening on address and port: 127.0.0.1:5353. We need to set OpenWRT to send DNS request to that address.
Server configuration
dnscrypt-proxy
The config file /etc/config/dnscrypt-proxy is simple and should be edited according to your needs. Possible values for the ‘resolver’ option are the first column in the list of public DNSCrypt resolvers.
config dnscrypt-proxy option address '127.0.0.1' option port '5353' # option resolver 'cisco' # option resolvers_list '/usr/share/dnscrypt-proxy/dnscrypt-resolvers.csv' # option ephemeral_keys '1' |
Description:
| Name | Type | Required | Default | Description |
|---|---|---|---|---|
address |
string | yes | 127.0.0.1 |
The IP address of the proxy server. |
port |
string | yes | 5353 |
Listening port for DNS queries. |
resolver |
string | no | cisco |
DNS service for resolving queries. You can’t add more than one resolver. |
resolvers_list |
string | no | /usr/share/dnscrypt-proxy/dnscrypt-resolvers.csv |
Location of CSV file containing list of resolvers. |
ephemeral_keys |
boolean | no | 0 |
Improve privacy by using an ephemeral public key for each query. Recommended if you are not using your own server. Ephemeral keys option requires extra CPU cycles and can cause huge system load. Disable it in case of performance problems. |
If you need to specify other options, you will have to edit the /etc/init.d/dnscrypt-proxy script.
Note: I’ve had a little bit of confusion at setup, so I want to remind you; address and port strings are for local proxy server, you just have to pick a dnscrypt server from the resolvers list, put its name in resolver string and comment out resolvers and resolvers list settings.
Now we will start DNSCrypt and enable auto boot for it:
/etc/init.d/dnscrypt-proxy enable /etc/init.d/dnscrypt-proxy start
Note: If dnscrypt-proxy is not starting after a router reboot, it may be trying to start before the network interface is fully up. Add the following to /etc/rc.local, above the line “exit 0”:
sleep 10 /etc/init.d/dnscrypt-proxy start
dnsmasq
Assuming you are using dnsmasq, edit the bold lines in /etc/config/dhcp
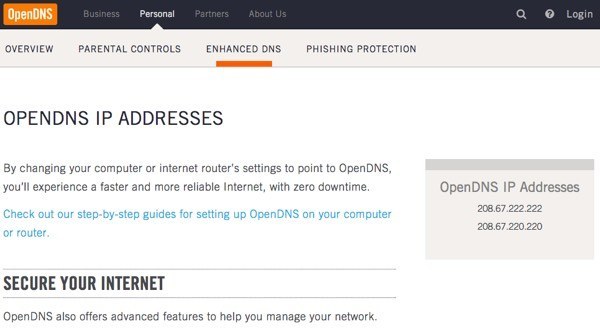
config dnsmasq option domainneeded 1 option boguspriv 1 option filterwin2k 0 option localise_queries 1 option rebind_protection 1 option rebind_localhost 1 option local '/lan/' option domain 'lan' option expandhosts 1 option nonegcache 0 option authoritative 1 option readethers 1 option leasefile '/tmp/dhcp.leases' # option resolvfile '/tmp/resolv.conf.auto' option noresolv 1 list server '127.0.0.1#5353' list server '/pool.ntp.org/208.67.222.222' # list server '208.67.222.222' # list server '208.67.220.220' |
-
We have disabled
/tmp/resolv.conf.autofile since it instructdnsmasqto use your ISP’s DNS. -
noresolvoption also disables/etc/resolv.conffile for similar reason. -
127.0.0.1#5353is the DNSCrypt address. -
/pool.ntp.org/208.67.222.222adds an exception for pool.ntp.org, which will be resolved through the standard unencrypted DNS channel. DNSCrypt requires precise time, otherwise it will not resolve any domain, including pool.ntp.org. So if your device’s time was incorrect, it could never update its time, and therefore DNSCrypt would never work. So we set this exception so that pool.ntp.org queries will always bypass DNSCrypt and resolve with the standard unencrypted OpenDNS method.
Reboot router or restart dnsmasq for the changes to take effect.
/etc/init.d/dnsmasq restart
Client configuration
Note: you may need admin privileges to run the commands below.
Linux
sudo /etc/init.d/nscd restart
or
sudo /etc/init.d/networking restart
Windows
ipconfig /flushdns
Mac OS X
-
Mac OSX 10.4 (Tiger)
-
lookupd -flushcache
-
-
Mac OSX 10.5/10.6 (Leopard/Snow Leopard)
-
dscacheutil -flushcache
-
Troubleshooting
How to check what features are supported by your resolver
-
The DNS leak test or DNS randomness test will show the actual IP of your DNS. You can check here if the IP is associated with the service you are using (put the IP in the search field).
-
DNSSEC resolver test determines whether your DNS resolver validates DNSSEC signatures.
-
If you can access DNSCrypt.bit, your resolver can resolve domain names using Namecoin.
How to check if your DNS queries are using dnscrypt
On the router:
pkill -STOP dnscrypt-proxy
DNS resolution should not work any more.
To restore service, unfreeze the client proxy:
pkill -CONT dnscrypt-proxy
How to check if dnscrypt-proxy is set up and running
The easy way is to look in the log.
-
Check if
dnsmasqis using only dnscrypt. Only the last block of logged nameservers is relevant.-
logread | grep -n "using nameserver"
-
132:Jan 1 01:01:00 openwrt daemon.info dnsmasq[1883]: using nameserver 208.67.222.222#53 for domain pool.ntp.org 133:Jan 1 01:01:00 openwrt daemon.info dnsmasq[1883]: using nameserver 127.0.0.1#5353
-
-
Check that
dnscrypt-proxyis working.-
logread | grep "Proxying from"
-
Jul 1 12:00:00 openwrt daemon.info dnscrypt-proxy[1831]: Proxying from 127.0.0.1:5353 to 208.67.220.220:443
-
Suspicious certificate received
A “suspicious” certificate can be reported:
root@OpenWrtRouter:/tmp# ./dnscrypt-proxy -R dnscrypt.eu-nl -a 127.0.0.1:5353 [INFO] Generating a new key pair [INFO] Done [ERROR] Suspicious certificate received [ERROR] No useable certificates found [INFO] Refetching server certificates [ERROR] Suspicious certificate received [ERROR] No useable certificates found |
Check the date and time on your router: this kind of behavior is usually caused by a system clock that hasn’t been set properly.